Chapter 4 ~ Rights, Privacy,
and Cybersecurity
In this chapter you'll explore rights, privacy, and security topics such as intellectual property, fair use, coders' rights, international and national privacy laws, types of threats, and threat legislation.
Then, you'll examine a case where privacy or security failed, discuss the laws involved, analyze the major player(s) in relation to an ethical theory, and counter another student's argument.
4.1 Introductions: Rights
Property Rights include real/physical and intellectual private ownership, public open access, public closed access, and government ownership. Real/Physical property includes land, homes, and physical items (Article V, Bill of Rights). Laws about search and seizure of physical and digital property change periodically and may affect your interactions with police at national borders.
Intellectual Property (IP) refers to creations of the mind, such as inventions (patents), works of art and writing (copyrights), trade secrets, and commercial symbols and imagery (trademarks). IP also allows Fair Use of a copyrighted work for certain situations. Brief excerpts of copyrighted material may, under certain circumstances, be quoted verbatim for purposes such as criticism, news reporting, teaching, and research, without the need for permission from or payment to the copyright holder. Some IP laws are internationally accepted and some are not.
Personal data in a database may or may not remain a person's property if they sign away their rights in a Terms of Service Agreement.
Software/data developers may have special rights or a lack of rights when it comes to their work. Accepting contracts with employers may require a lawyer's input to ensure both parties retain adequate rights to their creative works.
Explore these key concepts by reading one or more of the following:
Reading List
Refer to writing instructions under each page of the template provided in step 4.5. Open articles in new tabs and add them to your bibliography tool.
- Electronic Frontier Foundation (EFF): Know Your Rights regarding digital devices.
- Copyright sections of Intellectual Property law (USA).
- Patents (USA). See also, how to Protect Yourself Against Invention Promotion Scams.
- Trademarks (USA).
- Measuring Fair Use: The Four Factors article.
- The 'Fair Use' Rule: When Use of Copyrighted Material Is Acceptable. Mashups, remixes, quotations, parody, video/sound clips, and thumbnail images are also acceptable under fair use rules.
- Report on Legal Protection for Databases
- EFF's Coders' Rights Project section.
4.2 Electronic privacy.
Privacy is freedom from observation by other people, tracking by computers, or monitoring by companies and governments. Many country's laws include guidelines for maintaining, allowing, and prosecuting breaches of personal privacy. Explore this key concept by reading one or more of the following:
Reading List
Refer to writing instructions under each page of the template provided in step 4.5. Open articles in new tabs and add them to your bibliography tool.
- Privacy’s not an abstraction: An experiment in privacy–and the discussion that ensued–offer unexpected lessons in who gets watched, and how.
- EFF's International Privacy Standards section.
- Educational privacy (FERPA) Student data is private from parents, businesses, and school staff except for instructors and advisors. PDF.
- Medical privacy (HIPAA) A patient's data is private until insurance companies, family, employees and other health works are granted permission.
- Business privacy (ECPA) Third parties cannot disclose or intercept personal data without consent.
- Finance privacy (Gramm-Leach-Bliley Act) Bankers must provide security and confidentiality of customer data.
- Government privacy (The Privacy Act of 1974) The act has loopholes and needs overhauling.
- The Clarifying Overseas Use of Data (CLOUD) act refers to American and foreign law enforcement’s ability to target and access people’s data across international borders. (USA Department of Justice)
- Electronic Frontier Foundation (EFF)'s Mandatory Data Retention section.
- PATRIOT Act's loose rules about wiretapping and electronic surveillance.
- DuckDuckGo, EFF, and others just launched privacy settings for the whole internet.
- In tech, workers fight for transparency.
4.3 Cybersecurity.
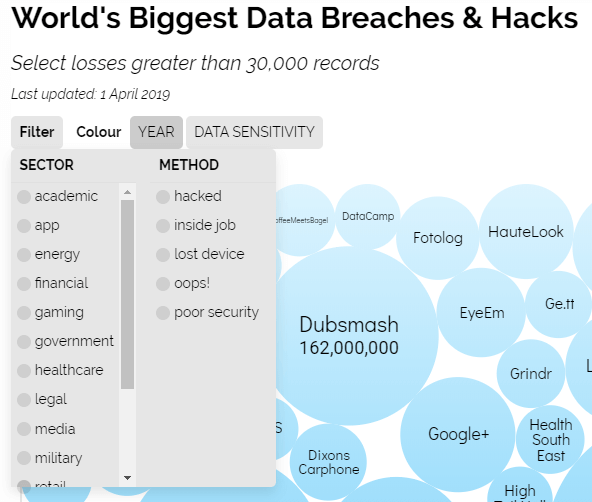
Kaspersky and other security companies maintain a network of more than 8 million sensors that
emulate over 6,000 applications which gather data on cyber attacks.
See which countries have the most cyber threats on their interactive
Kaspersky Lab Cyberthreat Real-time Map:
Hover over the scan acronyms to learn their names.
To understand cybersecurity and hackers, view these informative videos from Crash Course: Cybersecurity: Crash Course #31.
Hackers and Cyber Attacks: Crash Course Computer Science #32.
Reading List
Nearly every day we must contend with a new kind of malicious online act. These acts are dubbed with interesting names, which would take hours and hours to understand! Choose one to research. Refer to writing instructions under each page of the template provided in step 4.5. Open articles in new tabs and add them to your bibliography tool.
- Advanced Persistent Threads (APT)
- Backdoor
- Botnet
- Browser Hijack
- Brute Force
- Click Bait, Engagement Bait, Malvertising
- Cryptojacking
- Cross-site Scripting
- Cyberflashing
- Cyberwarfare
- Dark Patterns
- Deep Fake
- Dedicated Denial of Service Attack (DDoS)
- DNS tunneling
- Drive-by downloads
- Fileless Malware
- Geotagging
- Injection Attack
- Keylogging
- Man-in-the-Middle attacks
- NAND Mirroring
- Pharming
- Phishing and Spear Phishing
- Rainbow Table Attack
- RAM Scraper
- Ransomware
- Robocall
- Rogue Security Software
- Remote Access Trojan or Tool (RAT)
- Rootkit
- Spoofing, watering hole
- Spyware, Stalkerware, and Snooping (sound, video, webcam)
- Super-cookies, Evercookies, Zombie Cookies, Sidejacking
- Social Engineering, Pretexting
- Trojan Horses
- Worms
- Zero-hour Auto Purge (ZAP)
- Zombie computer
- Zoombombing
Did you discover a term that is not on the list? Share it in the Bug Bounty forum to earn extra credit.
4.4 Cybersecurity laws and organizational guidelines.
Besides devising ethical frameworks, computer scientists are working hard to devise solutions, technical guidelines, and laws to deter malicious acts as well as punish the bad actors. Do you think our current laws are doing the job? Explore laws by reading one or more of the following:
Reading List
Refer to writing instructions under each page of the template provided in step 4.5. Open articles in new tabs and add them to your bibliography tool.
- EFF's Computer Fraud And Abuse Act Reform section.
- EFF's Cyber Security Legislation section.
- National Institute of Standards and Technology (NIST) Cybersecurity Framework
- SANS Programs to mitigate cybersecurity problems.
- (ISC)² Certified Information Systems Security Professional (CISSP)
- Map of Data Protection and Privacy Legislation Worldwide from the United Nations Conference on Trade and Development (UNCTAD)
- The ICLG to: Data Protection Laws and Regulations (USA)
4.5 Set up the Template and Reading List.
Use the following template link to complete this research and writing assignment.
- Login to your OSU Google Account.
- Launch this chapter's
- Do not request permission to use the file. Login to your OSU Google Account.
- Once you have the file open:
- → .
- Rename the new file so it includes your "First and Last name" in place of "Template".
- Move the file into a folder for this course.
- Add your name to the cover page.
- Read instructions on the cover page. When in doubt about how to write in the templates, refer back to this page for clarification.
- Refer to the green instructions below each page to understand what is required.
- The last page requires a bibliography.
4.6 Edit, download, and submit the file.
- Ctrlc or ⌘c Copy the bibliographic entries you made during the Explore Topics reading and research. On the last page of the template, Ctrlv or ⌘v paste in the bibliographic entries. Select the list and apply the bullet or numbered list icon. Update the font size to 14 if necessary. Add more pages if necessary.
- Check and correct grammar and spelling using the built-in functions.
- From the menu, choose Download as PDF.
- Check to confirm that hyperlinks work in the new PDF file. If they do not work, then in the Assignment Commenting Box, leave a note stating which platform, operating system, and browser you used to print or download the PDF file.
- Copy the file to a backup folder on your hard drive.
- Submit the PDF file by uploading it in the Canvas Assignment screen.
- Confirm that your file has uploaded by looking for the document icon in the Grades area.